The core of the Xybern Execution Control Layer. Every AI output, from any model, any agent, any format, is intercepted, decomposed into claims, verified against evidence, and enforced before reaching users or systems.
Three pillars of the enforcement engine.
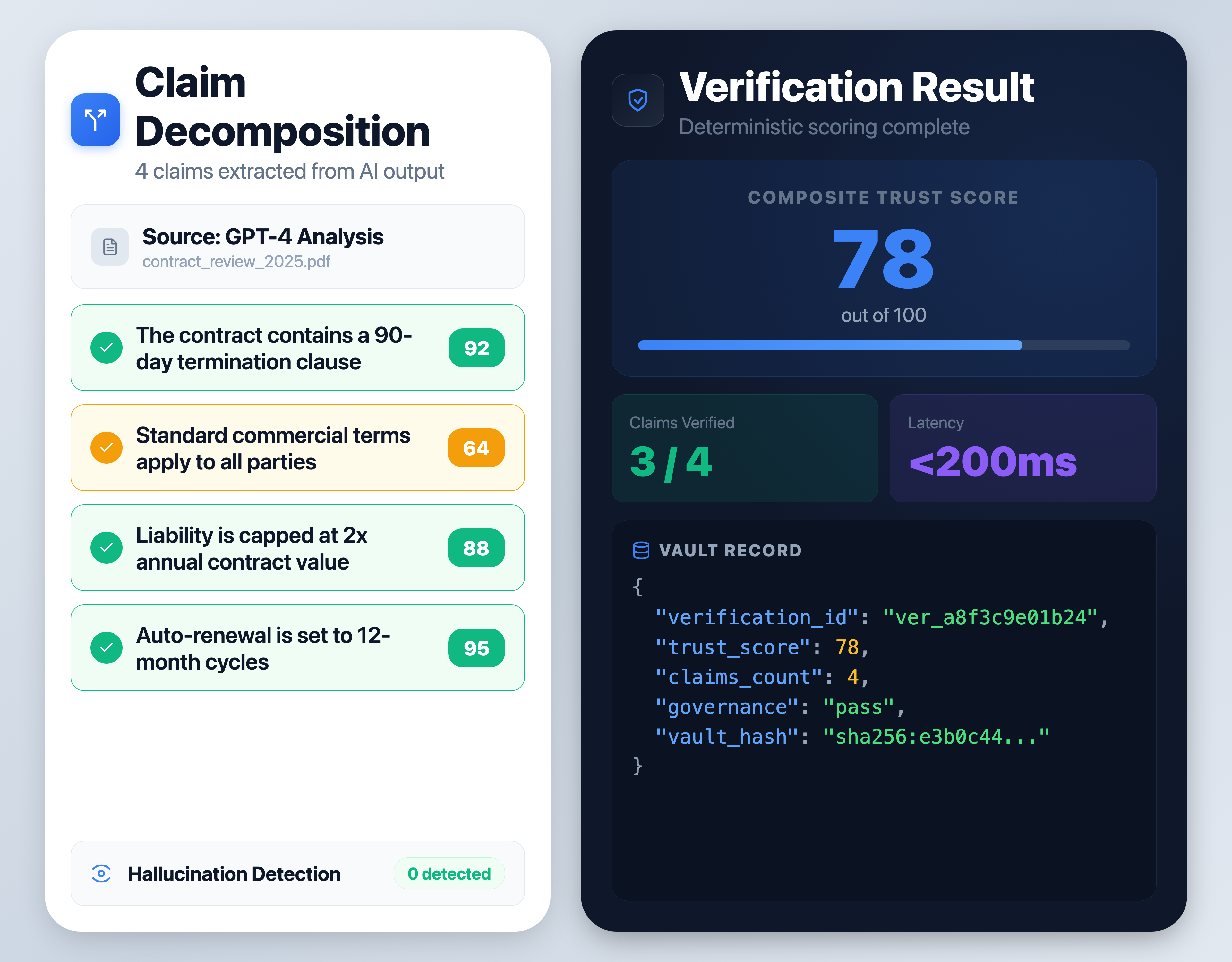
Every AI output is intercepted at the execution boundary and broken into individual, verifiable claims. Each claim is independently scored against source evidence, no black-box assessments.
A runtime verification engine that decomposes claims, maps evidence, and produces deterministic trust scores. Every output is anchored to original evidence, not model training data.
An immutable cryptographic ledger that records every enforcement decision, verification result, and trust score. Every entry is reproducible, auditable, and permanently anchored.
Send any AI output to POST /api/v1/verify and get back a deterministic trust score, claim-level breakdown, and a permanent vault record.
One API call covers runtime verification, enforcement, and vault recording. No orchestration needed.
Every response includes trust score, individual claims, evidence mapping, and enforcement outcome.
Scoped API keys with workspace isolation, rate limiting, and full access logging.
// POST /api/v1/verify { "content": "The contract contains a 90-day termination clause...", "source": { "type": "llm", "model": "gpt-4", "provider": "openai" }, "original_prompt": "Analyze this contract" } // Response { "ok": true, "verification_id": "ver_a8f3c9e01b24", "trust_score": 78, "claims": [ { "text": "90-day termination clause", "score": 92 }, { "text": "Standard commercial terms", "score": 64 } ], "governance": { "outcome": "pass" }, "vault_hash": "sha256:e3b0c44..." }
The Verification Engine is built for enterprise AI infrastructure where governance is mandatory. Every verification is cryptographically anchored and fully auditable.
Rigorous external auditing of all security controls.
Enterprise identity and granular access logs.
Strict logical separation of customer environments.
Every data touchpoint recorded in the Vault.